Comments (19)
Ok yeah. The next branch already makes it configurable for the non-csrf cookie. I'll add the sameSite in there as well and add config options for the csrf stuff as well as it appears needed.
from external-auth-server.
https://www.troyhunt.com/promiscuous-cookies-and-their-impending-death-via-the-samesite-policy/
New chrome release is coming, so SameSite is also needed for single sign-on scenarios, was about to open an issue but found this one :)
My colleague just added SameSite and Secure here
and in scrf cookie and seems to be working fine (maybe a bit more testing is needed, but initially looks good)from external-auth-server.
Ah! Very interesting. Should be pretty easy to make it an option. I'll see what I can get together this week as I'm traveling.
from external-auth-server.
No hurry, it's ready when it's ready ;)
Thank you for your efforts to try to continuously improve this project.
from external-auth-server.
I've added new parameters (cookie.httpOnly and cookie.secure) to manage this, try it out and let me know how it goes. It's currently in the next image tag until I merge to master and/or tag.
from external-auth-server.
Thank you very much.
The setting has been applied on the session-cookie only. The csrf-cookie still have the original httpOnly-flag. But I'm not sure whether both of them should be affected of not.
Anyway for the session-cookie it works very well.
from external-auth-server.
Ah, very good. The csrf should be fine left as is. I actually used to delete it but ran into some weird edge cases where certain proxies can't cope with it.
Did is solve your issues with HA?
from external-auth-server.
@travisghansen
My issues is partially solved. For the desktop environments it's solved, either with Chrome as well as with other browser.
Mobile is another story. If I use Firefox on my Android mobile, then it's more or less solved. It still goes very often the extra way to re-authenticate on google, but no 503 errors. With Chrome it's still the same. The first hour is okey, with no redirects or errors. After that, all requests to HA get redirected to Google and after the auth process I get a 404.
In my opinion is something truly wring with HA. I heard from others which try use some kind of auth portal in front of HA, that it's mostly not working properly.
I will invest some more hours this weekend to solve it.
from external-auth-server.
@mlushpenko do you have a branch somewhere I can review with your changes?
@dannyyy service-workers could be an interesting situation and may not mix too well. I'm interested to see where it goes. It's similar to a single page app...there are very specific requirements to make it a bullet-proof experience.
from external-auth-server.
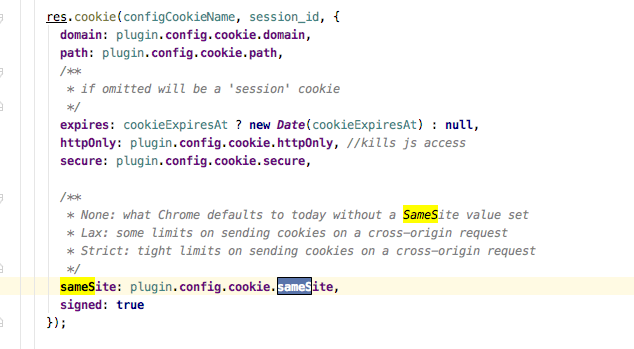
@travisghansen no branch, but here are the changes, you'll probably want to make it configurable.
diff --git a/src/plugin/oauth/index.js b/src/plugin/oauth/index.js
index b48632e..380121d 100644
--- a/src/plugin/oauth/index.js
+++ b/src/plugin/oauth/index.js
@@ -248,6 +248,8 @@ class BaseOauthPlugin extends BasePlugin {
{
expires: new Date(Date.now() + STATE_CSRF_COOKIE_EXPIRY * 1000),
httpOnly: true, //kills js access
+ secure: true,
+ sameSite: 'none',
signed: true
}
);
@@ -446,6 +448,8 @@ class BaseOauthPlugin extends BasePlugin {
*/
expires: cookieExpiresAt ? new Date(cookieExpiresAt) : null,
httpOnly: true, //kills js access
+ secure: true,
+ sameSite: 'none',
signed: true
});
from external-auth-server.
Ok, full control for managing cookies (csrf/session) has landed in next including the ability to completely disable the use of csrf cookie. This includes the settings for sameSite with a default of none for now.
Any review that can be done would be great before I snap a new release and merge to master.
Details are visible in this commit: f614542
from external-auth-server.
In my setup, the SameSite cookie doesn't get set.
The config is:
"csrf_cookie": {},
"cookie": {
"domain": "mydomain.com",
"httpOnly": true,
"secure": true,
"sameSite": "Lax"
},
from external-auth-server.
I'll test that config again. Are you sure you pulled the most recent next image?
from external-auth-server.
Yes
volker@volkers-mbp ~/external-auth-server > git checkout next
Already on 'next'
Your branch is up to date with 'origin/next'.
volker@volkers-mbp ~/external-auth-server > git pull git:(next|)
Already up to date.
from external-auth-server.
Are you checking the response in devtools? Here is what I see with your config above:
Set-Cookie: _eas_oauth_session=s%3Aa6311204-6ef1-4dbd-b144-16720b0994d3.znanrfRhPEyFcIwhML2DcEU2hgMRS9Uly%2FOKsTZW3ZU; Path=/; HttpOnly; SameSite=Lax
from external-auth-server.
This is the response from eas after successful auth:
content-length: 0
date: Fri, 28 Feb 2020 15:46:55 GMT
location: https://mydomain.com/
set-cookie: _eas_oauth_session=s%3Ac8c54ec5-8540-4649-83e8-9294d4bdadd3.tVNnIBtmE%2FfDwU7uj7FwiTZ3dg9XcKlVq1i%2BMEPzo8Q; Domain=verivinum.com; Path=/; HttpOnly; Secure
status: 302
X-DNS-Prefetch-Control: off
x-powered-by: Express
It is relay weird.
Git is definitely up-to-date:
from external-auth-server.
After starting the latest version of the docker image, the SameSite Cookie works!
Good work and thank's a lot!
from external-auth-server.
Nice!
from external-auth-server.
This has landed in master/latest.
from external-auth-server.
Related Issues (20)
- Bump jsonwebtoken from 8.5.0+ to 9.0.0+ to patch several moderate security vulnerabilities HOT 5
- GitHub Oauth Permission Write? HOT 13
- Traefik + EAS + KeyCloak HOT 10
- [BUG] uncaughtException: Cannot read properties of undefined (reading 'match') HOT 37
- Oauth2 support for Azure provider HOT 1
- Semi colons are replaced by ampersands after logout HOT 10
- Crash due to ERR_UNHANDLED_REJECTION HOT 2
- Question about cookie lifetime? HOT 2
- custom_service_headers not being injected HOT 8
- /metrics end point still available to access after set disabled HOT 9
- Crash at startup due to "unable to determine boolean value" HOT 1
- Using variable in redirect_uri HOT 6
- Environment variables HOT 12
- using yaml for token config HOT 27
- Fetch config_token like a Kubernetes Secret from Vault HOT 1
- Architectural question: does Traefik receive the token issued by eas? HOT 2
- No OIDC frontchannel logout when session_state is missing in the ID token HOT 5
- Limit number of concurrent OIDC sessions per user HOT 11
- Image vulnerabilities HOT 2
- EAS does not work with readOnlyRootFilesystem HOT 2
Recommend Projects
-
 React
React
A declarative, efficient, and flexible JavaScript library for building user interfaces.
-
Vue.js
🖖 Vue.js is a progressive, incrementally-adoptable JavaScript framework for building UI on the web.
-
 Typescript
Typescript
TypeScript is a superset of JavaScript that compiles to clean JavaScript output.
-
TensorFlow
An Open Source Machine Learning Framework for Everyone
-
Django
The Web framework for perfectionists with deadlines.
-
Laravel
A PHP framework for web artisans
-
D3
Bring data to life with SVG, Canvas and HTML. 📊📈🎉
-
Recommend Topics
-
javascript
JavaScript (JS) is a lightweight interpreted programming language with first-class functions.
-
web
Some thing interesting about web. New door for the world.
-
server
A server is a program made to process requests and deliver data to clients.
-
Machine learning
Machine learning is a way of modeling and interpreting data that allows a piece of software to respond intelligently.
-
Visualization
Some thing interesting about visualization, use data art
-
Game
Some thing interesting about game, make everyone happy.
Recommend Org
-
Facebook
We are working to build community through open source technology. NB: members must have two-factor auth.
-
Microsoft
Open source projects and samples from Microsoft.
-
Google
Google ❤️ Open Source for everyone.
-
Alibaba
Alibaba Open Source for everyone
-
D3
Data-Driven Documents codes.
-
Tencent
China tencent open source team.


from external-auth-server.